Solution for Surabaya Hacker Link Challenges
Well, this post was made because the Surabaya Hacker Link challenges have been updated and many people were curious about this challenge but hadn’t solved it yet and suggested making a video tutorial, but since I can’t make a video, I’ll just write it here instead, updated challenges
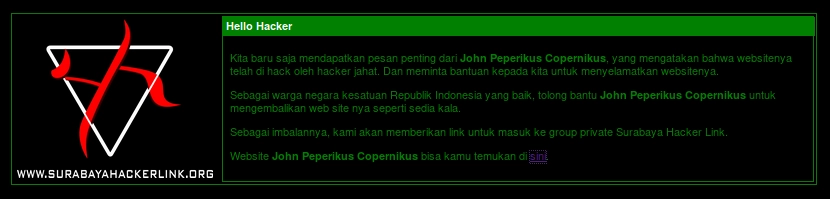
It explains that we have to save John’s website and then we will be given a Telegram group link (flag).
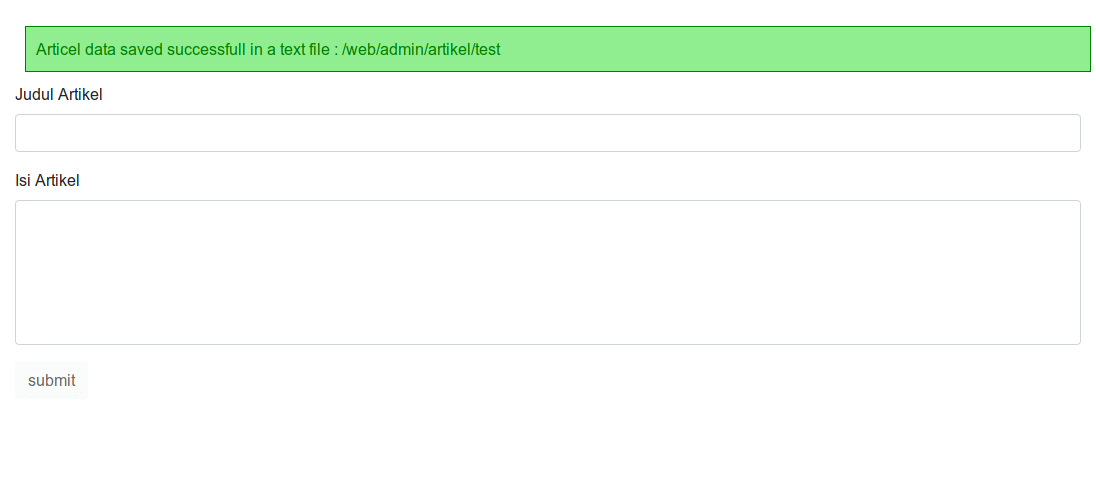
initial appearance of the shl challenge page
First, let’s try accessing John’s website.
the website has been defaced
As usual, we can use view-source: or ctrl+u to see if there’s something not rendered by the browser.
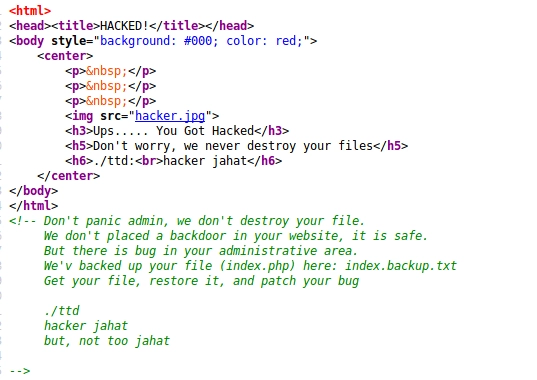
turns out there is an HTML comment from the evil hacker
We found information that there is a backup file index.php.txt which contains the original index of John’s website before it was defaced by the hacker.
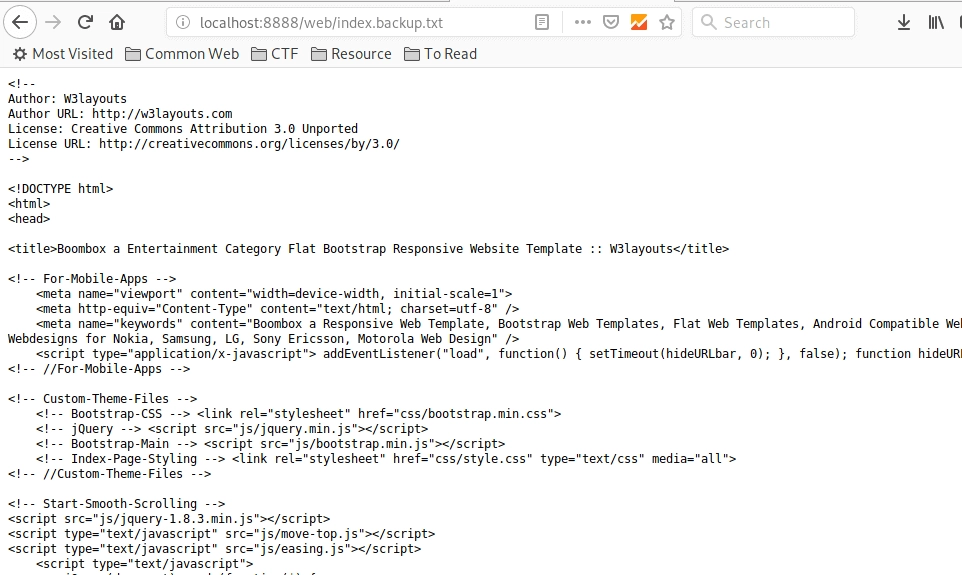
and there’s an implied message that the vulnerability is in the administration area, from the word “administration” we can assume it’s likely in the admin dashboard,
challenges.surabayahackerlink.org/web/admin
or
challenges.surabayahackerlink.org/web/administrator
yeah typical administration pages, then try accessing it
And it works
challenges.surabayahackerlink.org/web/admin
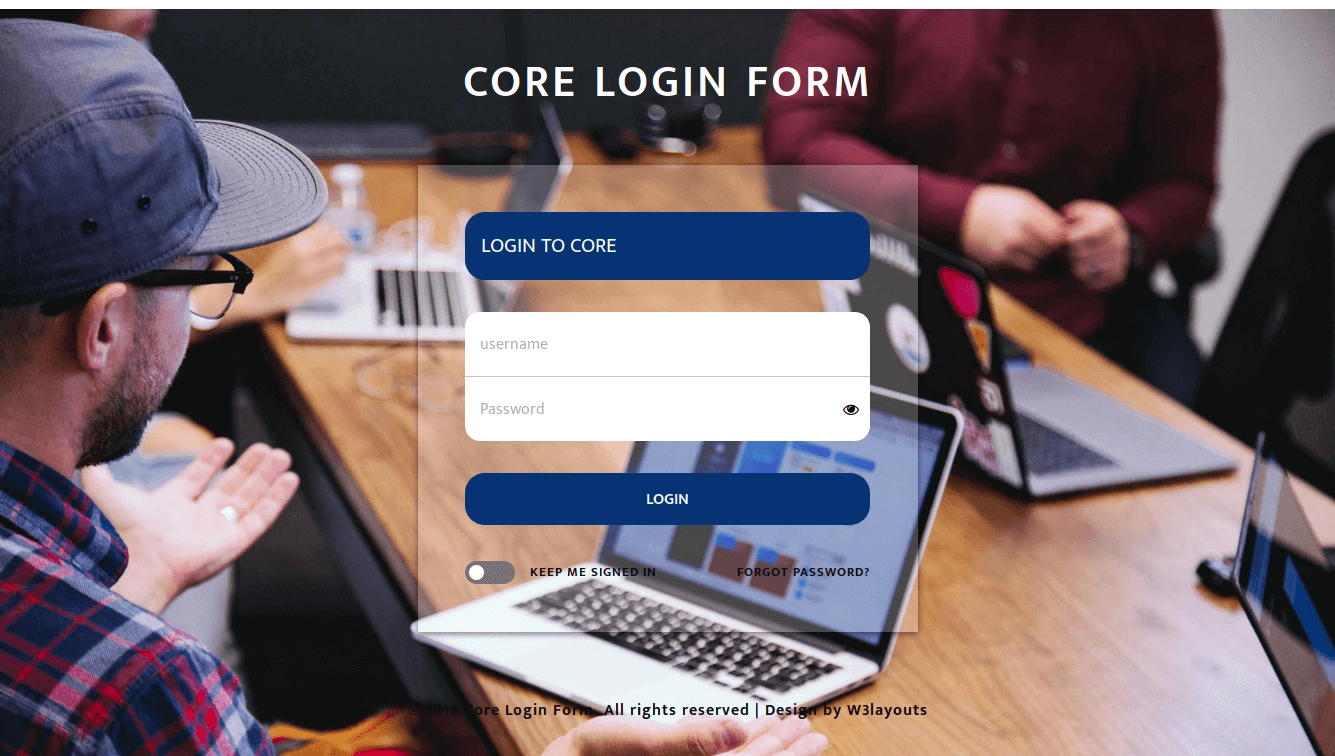
turns out there is a login form
We found a login form, then tried default admin:admin but failed, maybe guessed password isn’t the bug, let’s try inputting a quote.
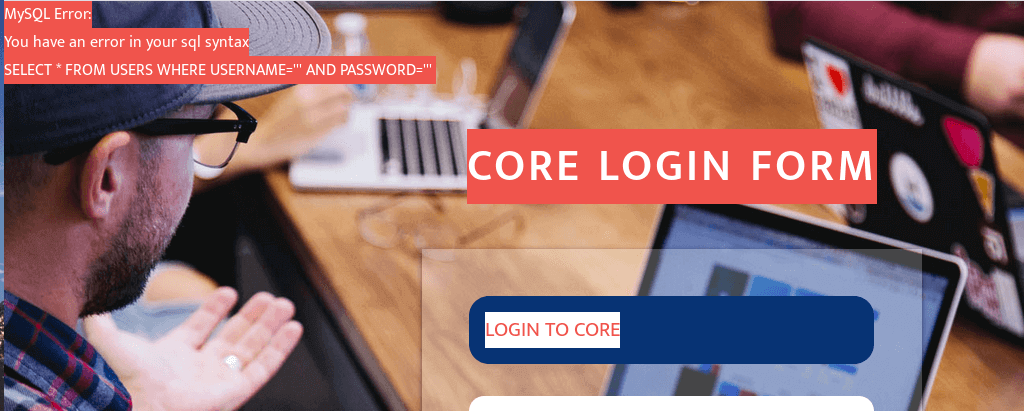
there is a query error message
So it’s likely this can be exploited with SQL injection, so let’s try common SQL injection payloads to bypass login.
Yay we successfully logged in.
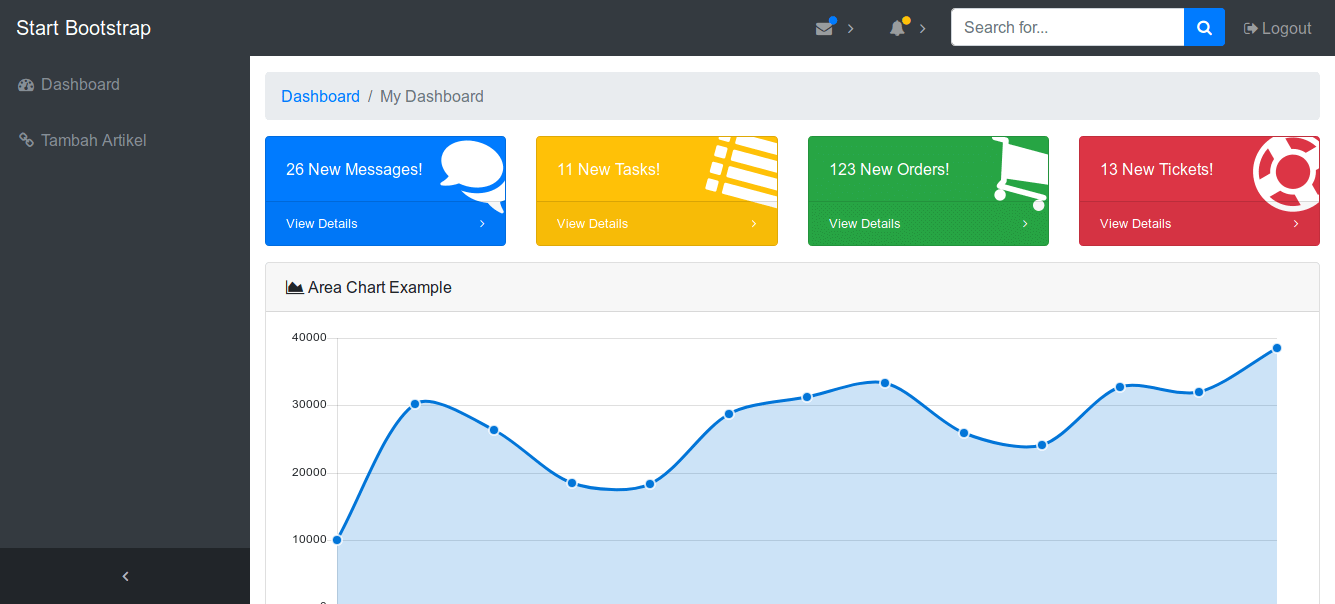
entered admin dashboard
What next?, oh right don’t forget the mission/goal — saving the website. If there’s no backdoor it can be considered saved, but the page still shows hacked by hacked by, so we need to restore the website display like the original. What was the original like? We got the backup file earlier :D
Let’s try the available features first.
turns out it’s stored as a file, not in a database
From here we can assume we can overwrite the hacked file with a new file, but after trying it turns out our file is only stored in the directory /web/admin/artikel/<here>, hhmmm..
Let’s try going back aka directory traversal , meaning we need to go back 2 directories. If you’re used to terminal bungurasih you’ll understand how to go back directories — yep using ../, so we need to overwrite the old index.php with the new one.
But we must go back 2 directories, final payload becomes ../../index.php and the article content is the backup file we found earlier.
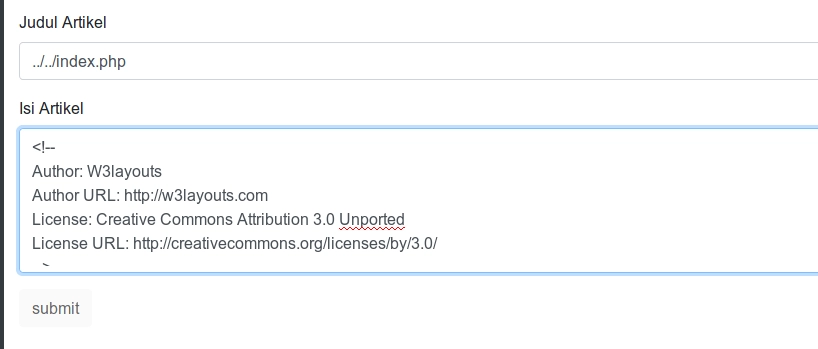
yay the old index file has been overwritten
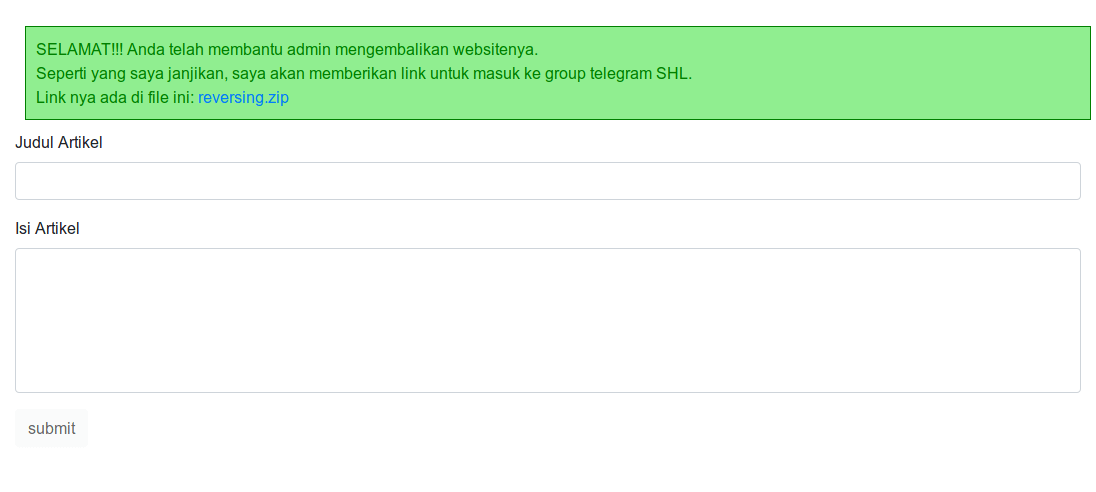
Wait, we’ve restored the website but why haven’t we gotten the flag (group link) yet?, turns out we’re still given a challenge in the form of an executable file (ELF) that must be reversed.
Let’s check the file architecture and whether it’s stripped, then try running it.
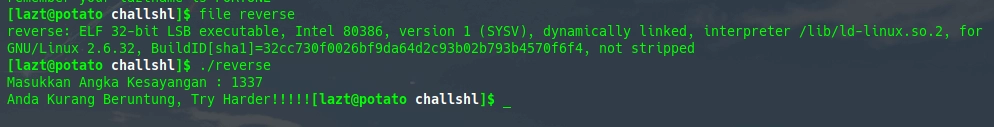
turns out it’s 32-bit, not stripped and fails with the favorite number 1337
Without hassle we just open it with ida and look at the pseudocode.
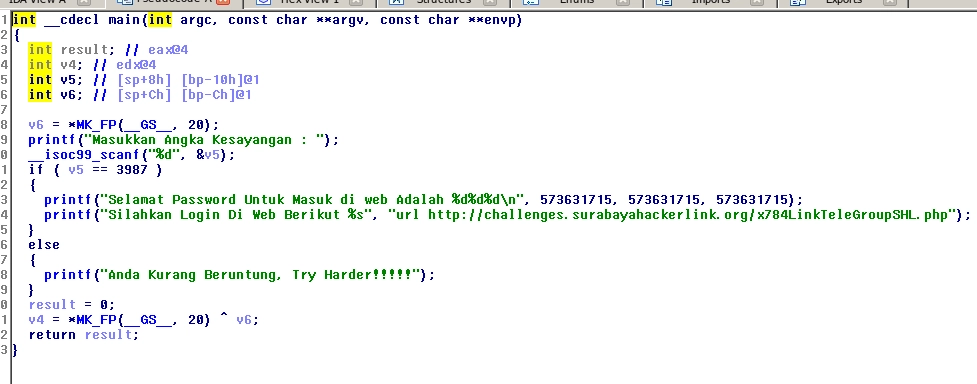
that’s roughly the original source of the ELF file we got earlier
It can be understood that the ELF reads user input (scanf with user input assumed as var v5), and there is a check if var v5 = 3987 then it will print congratulations blah blah and if not then you’re unlucky.
Run the ELF again and input the favorite number 3987.
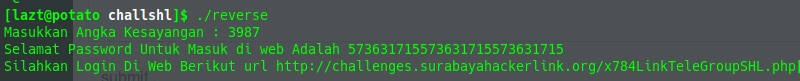
success
we get a key 5736** and a link
Access the link.
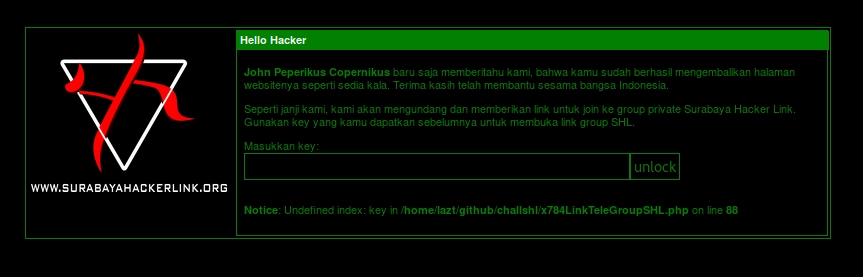
Enter key 5736**.
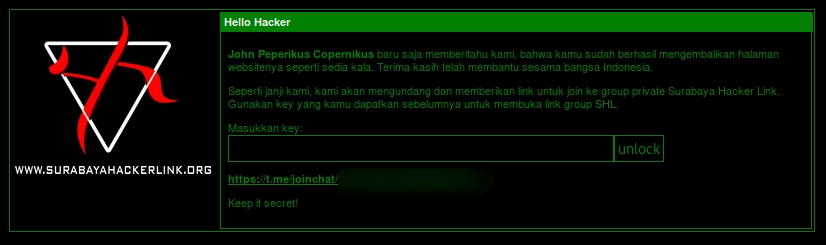
Congratulations we got the flag (Group Link), but keep it secret
That’s roughly how to solve this challenge
- Fin
