Interesting or Suspicious Ads Continued
After writing about malware ads using the Google Bard lure, now there is another malware ad that is slightly different, both in terms of the lure and the malware being delivered. This ad promotes a custom Windows taskbar to make it look more attractive. However, the file downloaded is actually malware and there is no custom taskbar installation as advertised. So what does the downloaded file install? Of course, malware. Below is roughly what the installer does.
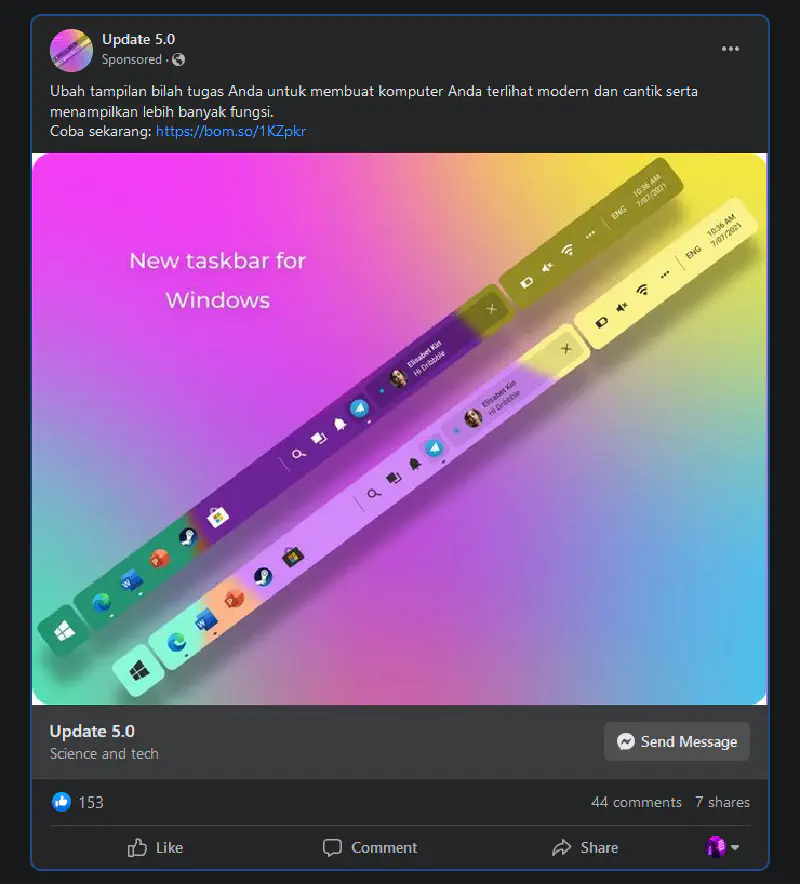
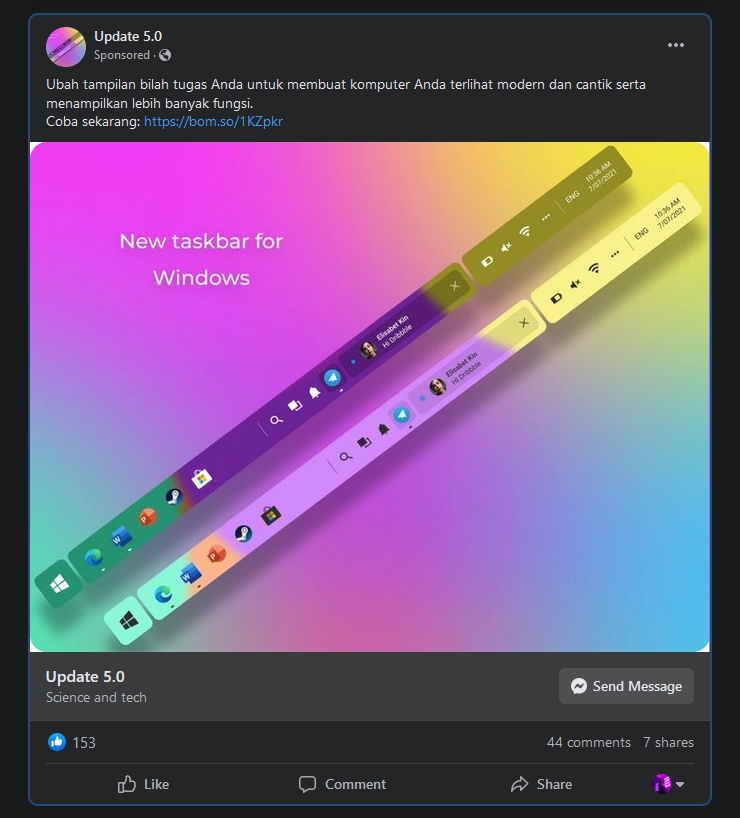
Here is the appearance of the ad. It looks attractive and can easily grab the attention of young users who want to customize their taskbar.
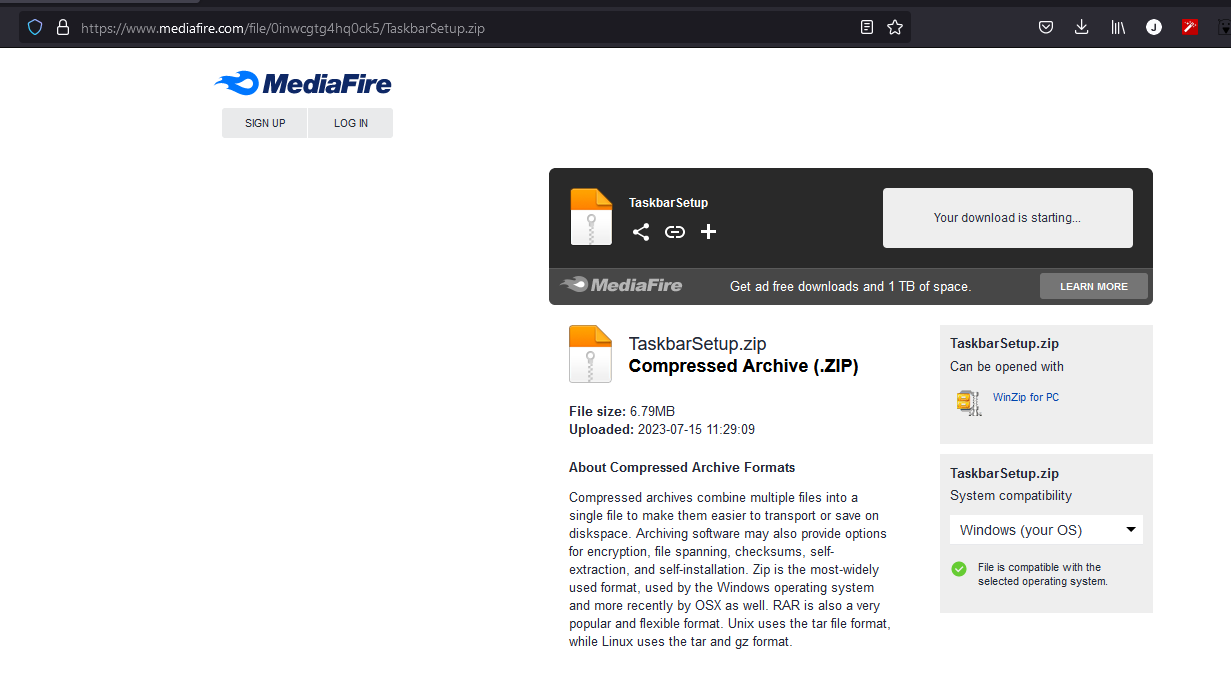
When clicking the ad, it redirects directly to a file hosting service called Mediashare. As usual, the delivered file is a password protected zip file. This technique is commonly used so that the malware inside the zip cannot be scanned by the file hosting provider’s antivirus.
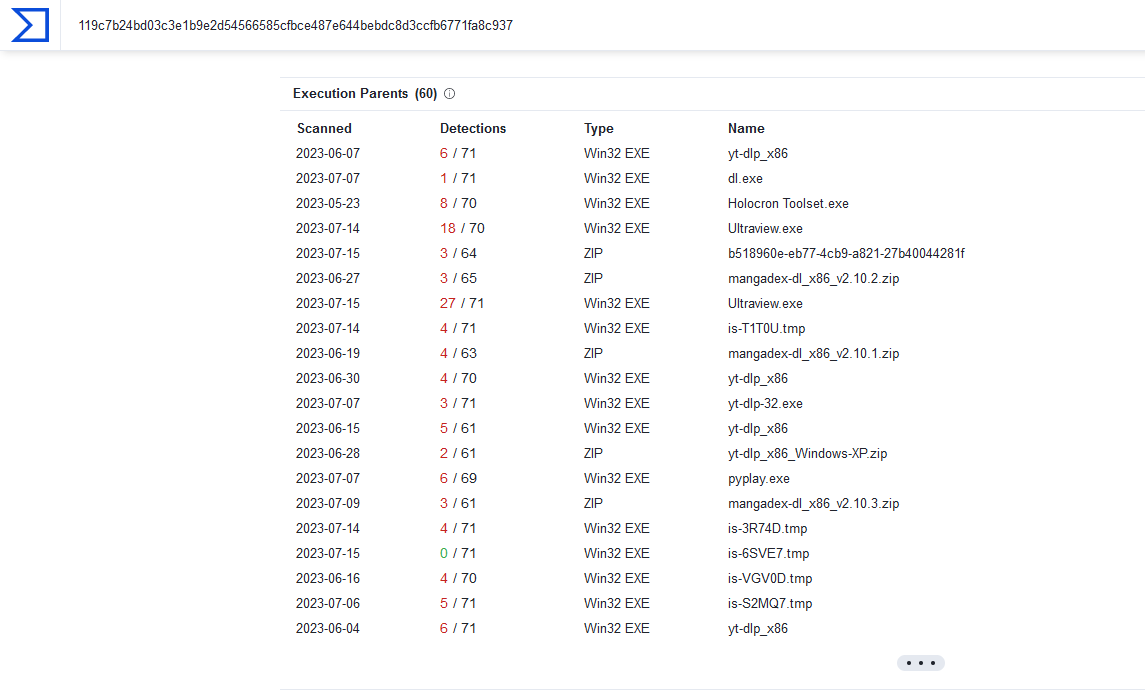
When checking the file taskbarsetup.exe, it was already heavily flagged on VirusTotal.
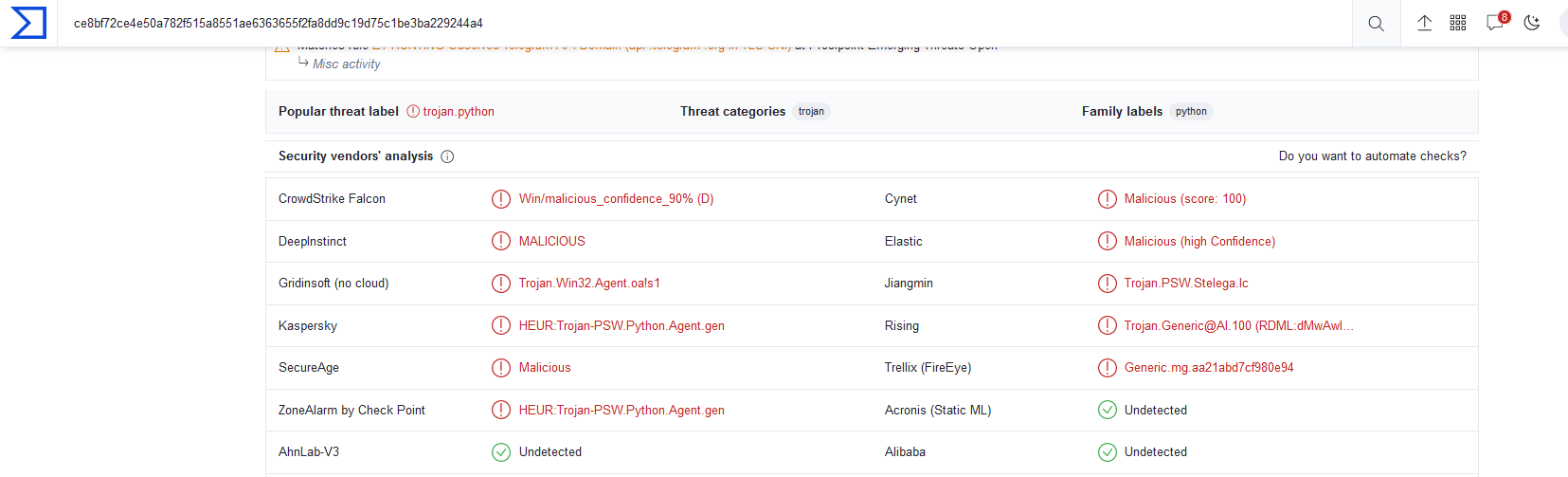
In the VirusTotal information, there are links connecting taskbarsetup.exe to several related files.
When installed, it displays a normal installation process.
The file taskbarsetup.exe drops a file named ultraviewer.exe and creates a directory named task in C:/.
When ultraviewer.exe runs, it performs a taskkill on the chrome.exe process.
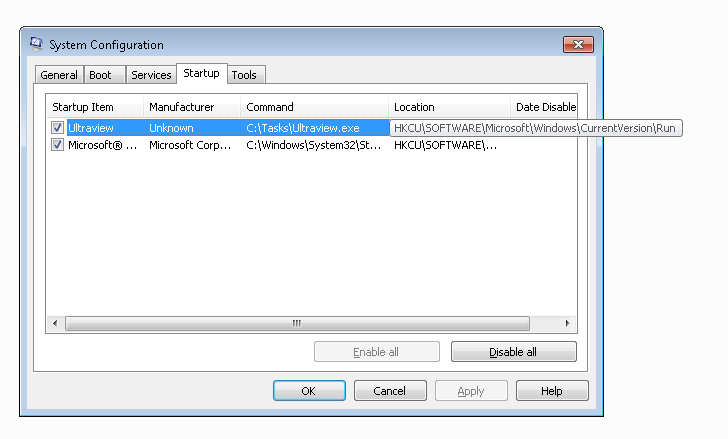
This malware also creates a startup entry in the Windows system.
The malware steals data such as browser cookies, especially from Chrome, files located on the desktop, and passwords stored in the Windows system.
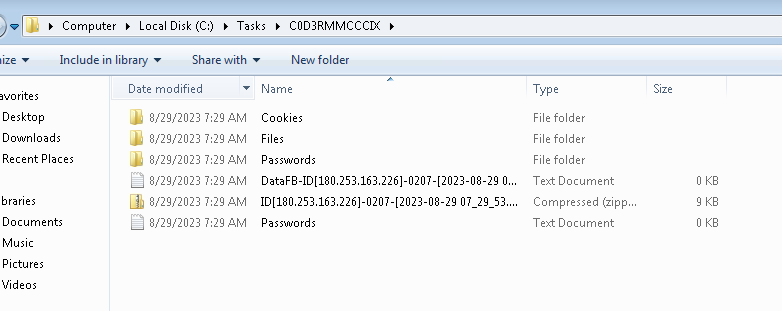
The stolen files are sent using a Telegram bot. From network monitoring, the file destination address can be observed.
As for the promised customization software, it does not exist at all.
Lesson Learned
Do not immediately trust advertisements. Always double check.
Review startup entries on your computer. If there is anything suspicious, remove it.
Do not install applications carelessly.
It seems that Facebook needs to improve its community standards enforcement.
Do not be too FOMO.
Note
This analysis is only a basic investigation driven by curiosity about what data the malware sends. It is possible that the malware performs additional actions that are not covered in this simple analysis.
