Hacking Phishing-as-a-Service

You may have just clicked on a Phishing Ad
I am tired of the ads that appear while watching reels on Facebook. Besides malware ads and online gambling ads, there are also many phishing ads targeting games like Free Fire and Mobile Legends, as well as ads inviting users to join 18+ groups. These ads are designed to steal social media account credentials and can seriously harm users.
Phishing, or password fishing, is a method widely used by threat actors to obtain access or credentials to services such as social media platforms like Facebook, TikTok, Instagram, WhatsApp, and others. After gaining access, accounts are often used for other malicious activities.

Before discussing today’s Phishing-as-a-Service, you may have heard of 16Shop, a phishing kit created by an Indonesian individual who was eventually arrested by authorities working with Interpol. The case discussed here is similar. They sell a service to create phishing websites through a self-service model.
Long story short, after seeing phishing ads on Facebook reels, I conducted a simple analysis. By exploiting a feature that was not properly validated, I managed to gain access to parts of their network.
On one of the subdomains, there was a website functioning as a store for creating phishing websites.
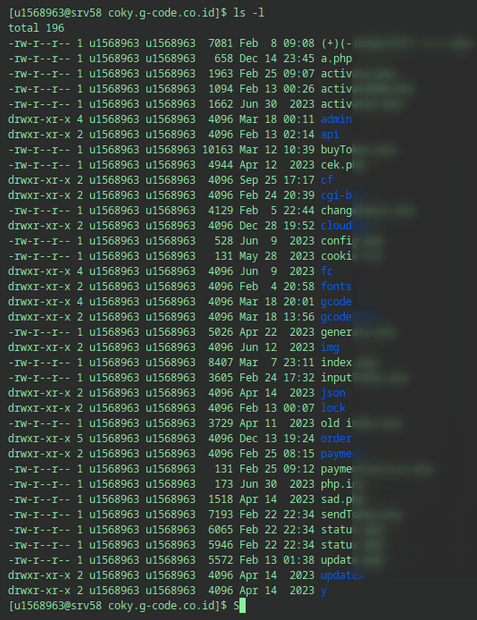
Based on file information, this group has likely been operating since mid-2023.
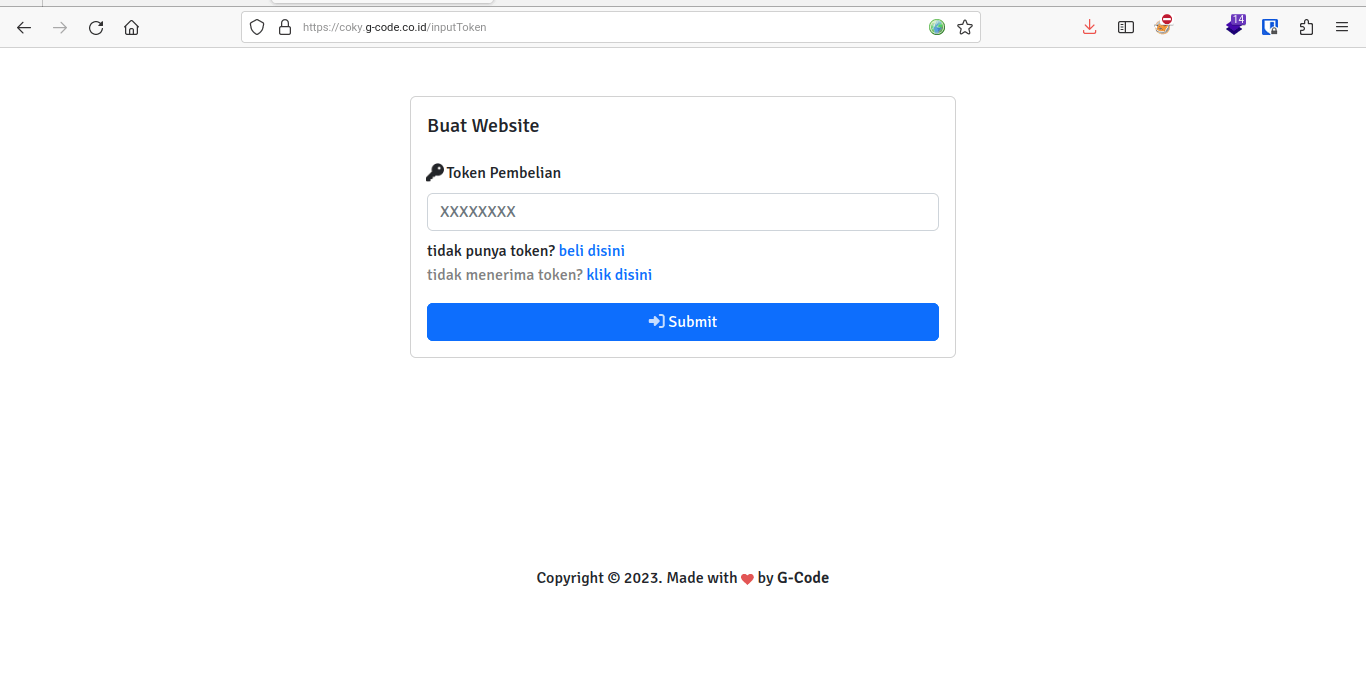
There is a paid website builder for phishing pages. By paying 10,000 IDR via QRIS, users are redirected to create the phishing theme they want.

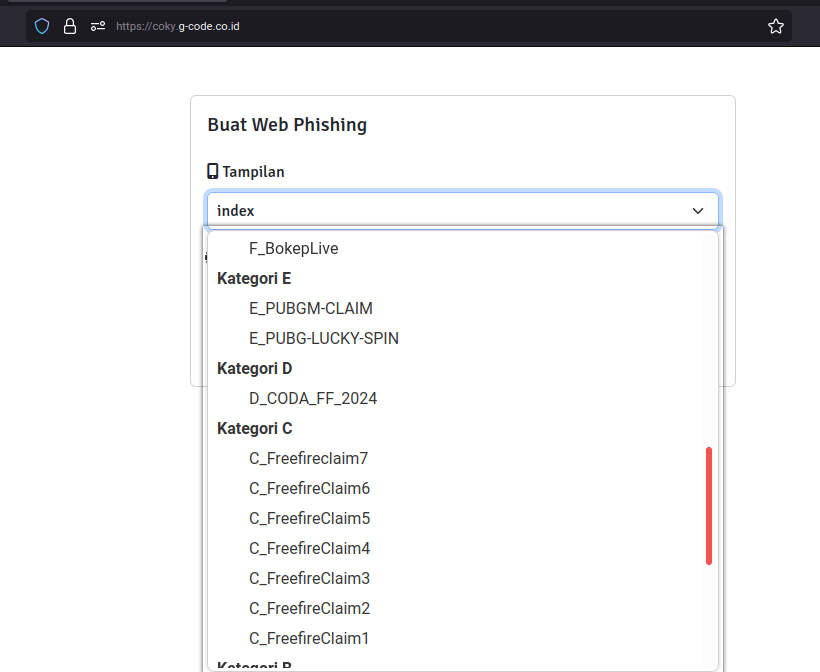
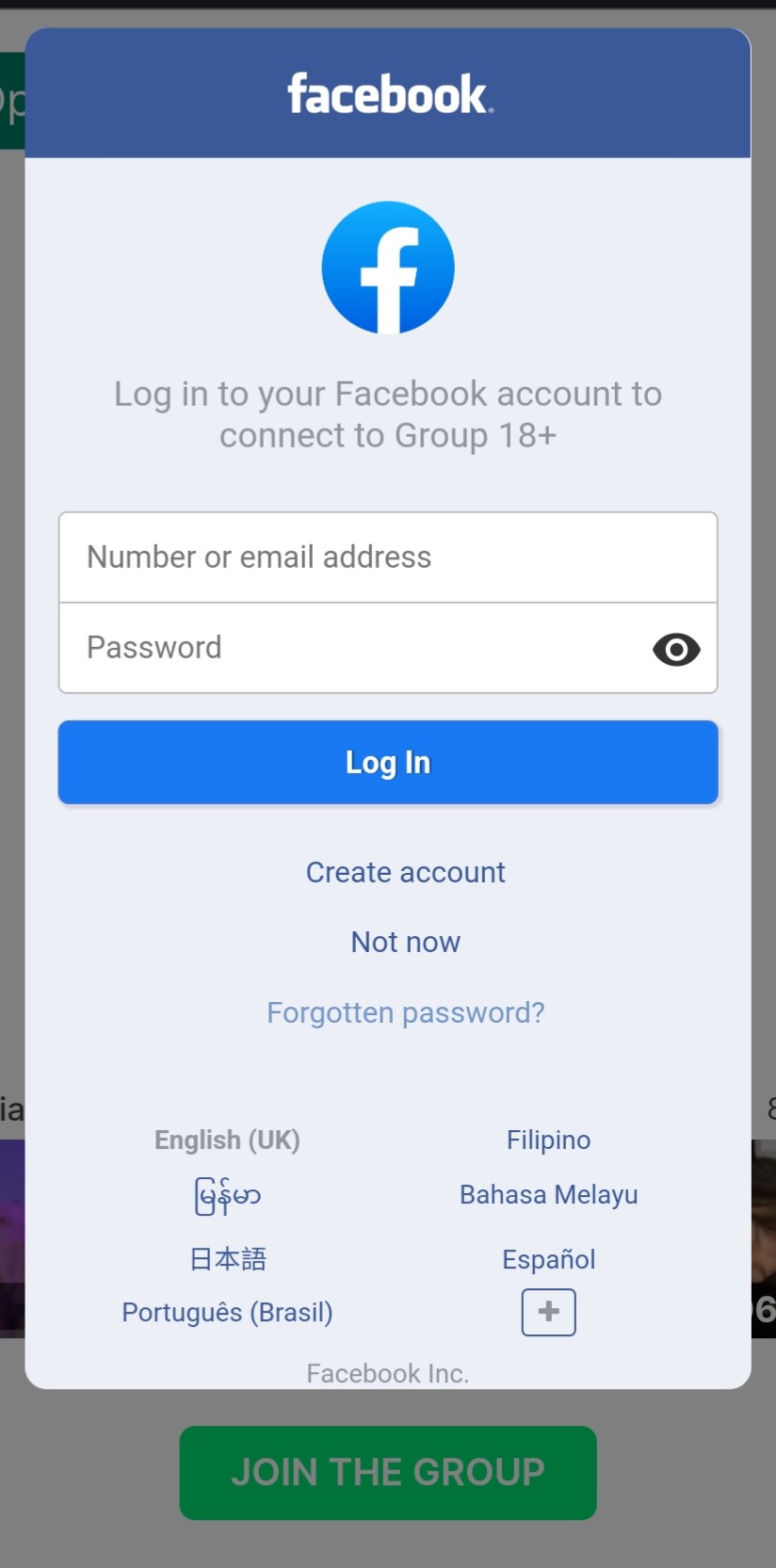
There are many phishing templates available, referred to here as lures. These include free in-game items, free game top-ups, free cheat downloads, free MediaFire downloads, and invitations to join 18+ groups.
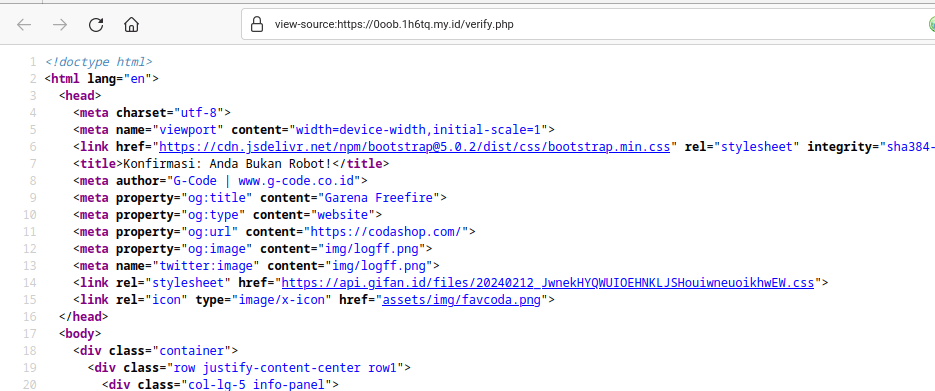
After successful setup, a verification page is displayed.

Once the phishing page is ready, buyers spread it using social media ads.
The phishing mechanism works like most phishing websites by sending victim input data to the attacker’s email. However, the self-service feature makes it Phishing-as-a-Service. It also includes a bot verification feature to avoid detection as a deceptive site when promoted through social media ads. The lure and delivery are quite subtle. When victims are attracted by the lure, a Facebook login pop-up appears, and victims may unknowingly enter their credentials.
We also managed to gain access to their phishing panel and servers.
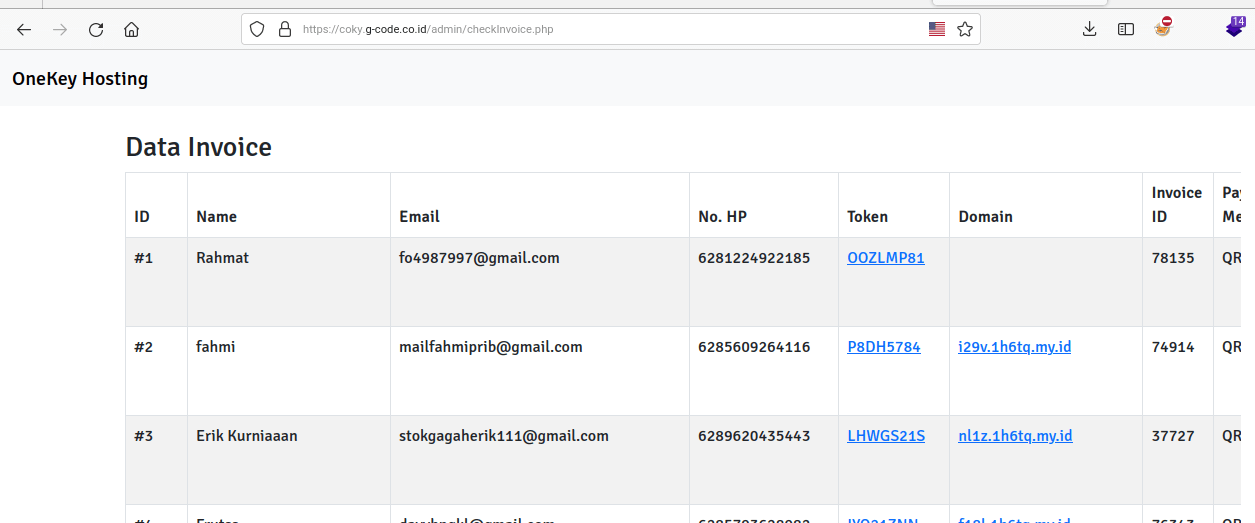

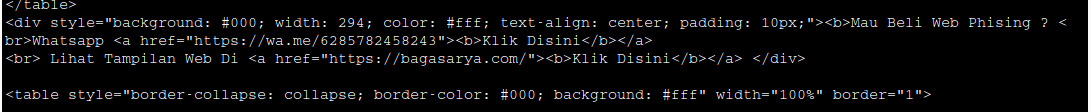
Further analysis revealed footer information in phishing result emails pointing to the domain bagasarya[.]com, used as the storefront. After purchasing, users are redirected to coky[.]g-code[.]co[.]id. Other phishing files also referenced a marketplace domain promoting this Phishing-as-a-Service operation, namely ezzystore[.]my[.]id.
The storefront runs on Niagahoster hosting for purchasing and self-service functionality.
The purchasing application creates subdomains from domains registered on another WHM server that has been configured beforehand.
The WHM server currently in use is hosted on Hetzner with IP 5.78.115.183 and is registered under the domain eren[.]busana[.]my[.]id.
See the archive here (warning explicit content).
Additional information about the owner of this Ph-aaS operation can be found via WHOIS history of bagasarya[.]xyz and ga-pedia[.]com using https://osint.sh/whoishistory/. Currently, their operation appears to be disrupted due to this exposure.
Lesson Learned
- Do not immediately trust information spread on the internet, especially through social media ads
- Do not be too FOMO
- Always double check everything
- Make sure your social media accounts are secure by using strong passwords and enabling 2FA
Fun Fact: If you came here without any reason, maybe you just clicked on a phishing ad.
