Anti-Gacor: Prevention and Protection Against Online Gambling Slot Injection on Websites

Introduction
In recent years, online gambling content injection attacks have surged significantly. Known by some groups as “slot gacor injection” or “judol (judi online/online gambling) attacks”, these have become one of the most disruptive threats for website administrators in Indonesia. Countless government agency websites, universities, and trusted institutions have fallen victim.
This article provides a comprehensive overview: what slot gacor is, how these attacks work, and how to prevent, detect, and recover from a compromised website.
What Is Slot Gacor?
Slot gacor is a term for illegal online gambling games based on slots that are aggressively promoted on the internet. Those running these online gambling operations don’t just advertise through normal channels, they also actively hack other people’s websites to spread their promotional content. They specifically target sites with high domain authority such as .edu, .ac.id, .go.id domains, and websites with high Domain Authority (DA) and Page Authority (PA), making the attack surface quite broad.
Why Is Our Website a Target?
There are several key reasons why attackers perform these injections:
- Boosting visibility - Gambling content placed on a trusted domain ranks more easily on the first page of Google.
- Funneling potential players - Any visitor who clicks a link or is redirected ends up on the attacker’s actual gambling site.
- Financial motivation - More players mean more profit.
- Domain quality -
.edu,.gov, and high DA/PA domains are highly valued by search engines, making them prime targets.
How Does the Attack Work?
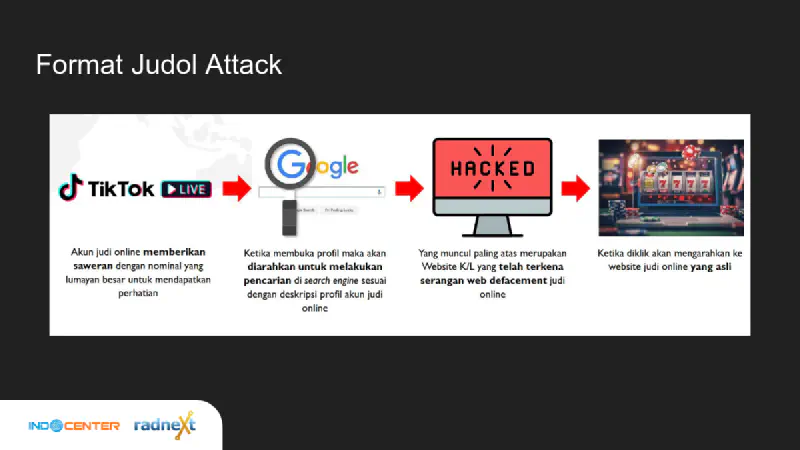
Attack Pattern (Judol Attack Flow)
The attack typically follows this pattern:
- An online gambling account on social media platforms like TikTok Live sends large virtual gifts to attract attention.
- Viewers are directed to open the account’s profile, which contains a description filled with online gambling keywords.
- The profile description instructs viewers to search for specific keywords on Google.
- The top Google search results display institutional websites that have been defaced.
- When clicked, visitors are redirected to the actual online gambling site.
How Attackers Gain Access
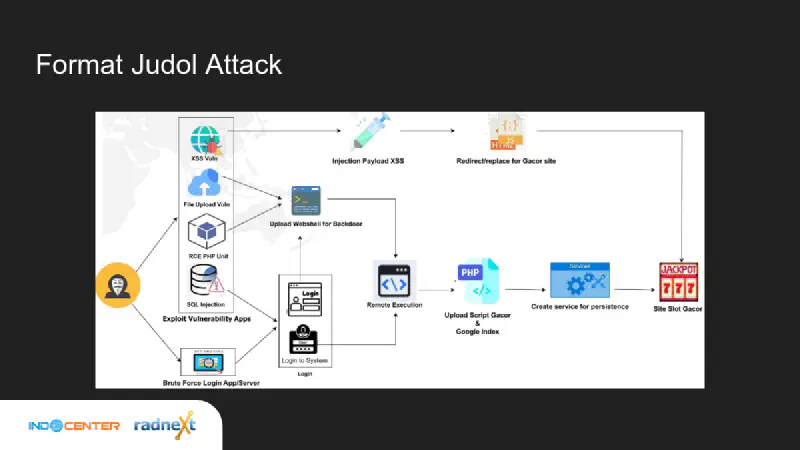
Attackers use various techniques to gain access to victim websites, including:
For WordPress and common CMS platforms:
- Weak passwords targeted with brute force
- Plugins or themes with security vulnerabilities (vulnerable plugins/themes)
- Pirated/nulled plugins or themes with pre-installed malware
- Infected hosting environments
- Server misconfiguration
- Zero-day exploit exploitation
- Credentials leaked via stealer malware
For non-CMS or custom framework applications:
- Weak passwords + brute force
- SQL Injection vulnerabilities
- Unrestricted File Upload vulnerabilities
- Exploitation of frameworks/libraries with known CVEs
- Misconfiguration
- Leaked credentials / stealer malware
Types of Slot Gacor Injection
Once access is obtained, attackers typically perform one or more of the following injection types:
| Type | Description |
|---|---|
| File Planting | Storing PHP webshell files or gambling content in the website’s directories |
| Backlink / Hidden Backlink | Embedding hidden links to gambling sites in HTML code |
| Redirect | Automatically redirecting visitors to a gambling site |
| Google Index Spamming | Creating fake pages/URLs indexed by Google with gambling keywords |
| Persistent Access | Creating backdoors or system services to maintain long-term access |
Impact of the Attack
This attack is far more than just inappropriate content. The consequences can be severe:
- Domain reputation damage - Google and other search engines will flag the website as dangerous, causing it to disappear from search results.
- Organizational reputation collapse - The public loses trust in the institution or organization whose website was hacked.
- Server abuse - The server can be used to host malware, botnets, and other malicious activities, potentially leading to server suspension or termination of service.
- Domain takedown - PANDI (Indonesia’s Internet Domain Name Manager) can suspend
.iddomains identified as containing negative content, often with very short notice.
When a website is hacked this way, the CIA Triad — Confidentiality, Integrity, Availability has been compromised.
Other Attack Vectors
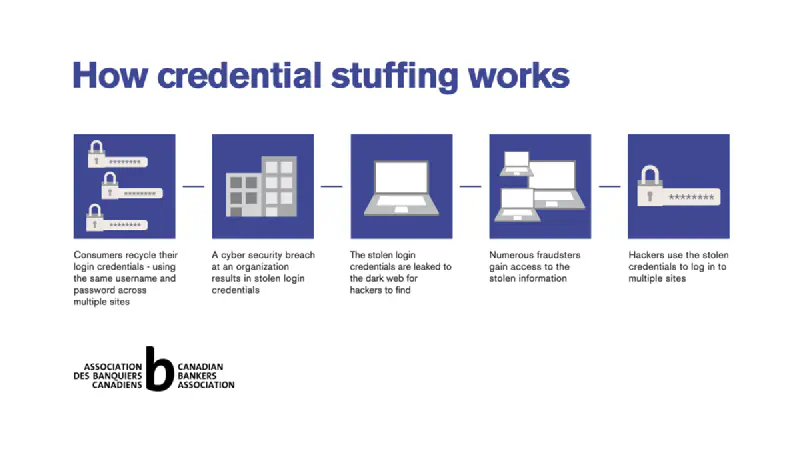
A security analyst once said: “Sometimes hackers don’t hack, they log in.”
This means not all attacks involve complex technical exploits. Other vectors to watch out for:
- Infected devices - Computers that store passwords in browsers and are infected with infostealer malware will silently steal those credentials.
- Leaked passwords - Credentials already in data breaches and sold on the dark web or hacker forums.
- Insecure hosting - Hosting providers that don’t implement adequate security can become an entry point for cross-account compromise.
- ClickFix attacks - Users are tricked into running malicious commands disguised as a CAPTCHA or fake security verification, which actually executes malware.
- Leaked API/SSH Keys - Access keys accidentally published in public repositories or other media.
Prevention: Better Safe Than Sorry
For WordPress and Similar CMS
- Use strong authentication and enable MFA (Multi-Factor Authentication) - This is the most effective layer of defense.
- Use a security plugin - Such as Wordfence, iThemes Security, or Sucuri.
- Choose hosting with built-in security features - Providers that offer Imunify360 or server-side antivirus.
- Disable the PHP engine in the uploads directory - Add
.htaccesswithphp_flag engine offin thewp-content/uploads/folder to prevent webshell execution from uploaded files. - Implement a security perimeter - Use a WAF (Web Application Firewall) like Cloudflare.
- Perform regular checks (weekly maintenance) - Monitor recently modified files, new admin accounts, and access logs.
- Build a SIEM or enable File Integrity Monitoring - Tools like Wazuh can detect suspicious file additions in real-time.
- Don’t save passwords in your browser - Use a password manager like Bitwarden or 1Password.
For Non-CMS / Custom Framework Applications
- Use strong authentication and MFA
- Apply Secure SDLC and Secure Coding - Input validation, parameterized queries, output encoding.
- Unit Testing - Ensure each component is tested for security.
- Penetration Testing - Conduct regular penetration tests by a third party.
- Implement a security perimeter (WAF, IDS/IPS)
- Regular monitoring and maintenance
- File Integrity Monitoring and SIEM
- Don’t save passwords in your browser
Detection: Has My Website Been Infected?
There are several ways to check whether your website has been injected:
1. Google Dorking
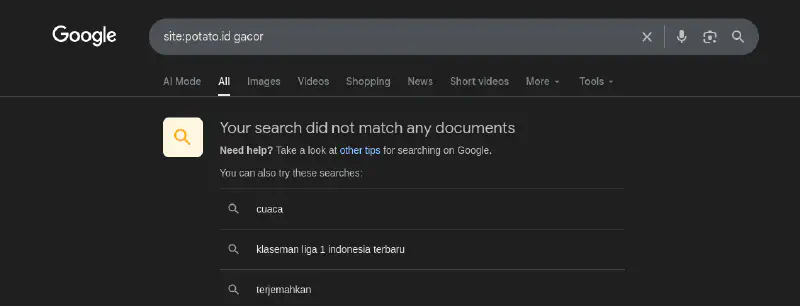
Search on Google using these queries:
site:yourdomain.com gacor
site:yourdomain.com slot
site:yourdomain.com judi
If strange pages with gambling keywords appear, your website has been compromised.
2. Google Search Console
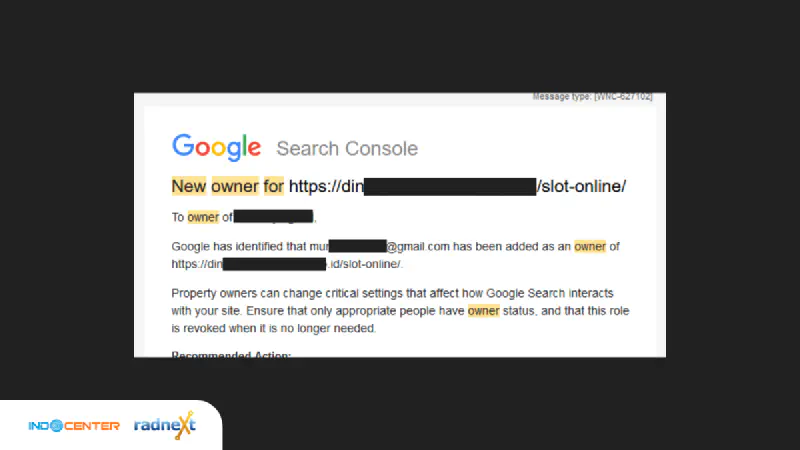
- Register your website at Google Search Console.
- Monitor notifications — Google will send alerts if it detects malicious content or an unrecognized new property owner.
- Watch for notifications like “New owner added” that you didn’t initiate yourself.
3. Domain Reputation Check
Use free services to check whether your website is safe:
4. Antivirus Scan
- Use ImunifyAV+ (available in cPanel hosting) to scan for malicious files.
- Run scans regularly and pay attention to files flagged as
php_malware.
Recovery: Steps After an Injection Attack
The recovery process requires more time and resources than prevention. Here are the steps:
- Isolate / Maintenance Mode - Disable public internet access to the website while the investigation and recovery process is underway.
- Change All Credentials - CMS admin passwords, cPanel, FTP, database, SSH, and all related accounts. Do this from a clean device.
- Check for Unknown Persistence - Review cron jobs, new admin users, unknown plugins, suspicious SSH connections, and unusual running processes.
- Log Hunting - Analyze access logs and error logs to identify the attacker’s entry point and the time of the incident.
- Backdoor Hunting - Search for webshell files or malicious scripts left behind. Tools like
grep -r "eval(base64" .can help. - Vulnerability Finding - Identify the security vulnerability that was exploited.
- Patch Vulnerability - Fix the vulnerability, update plugins/themes/CMS, and fix misconfigurations.
- Verify the Patch - Confirm the fix is effective and no backdoors remain.
- Re-publish - Restore public access to the website once it has been confirmed clean.
Lessons Learned
From the many cases that have occurred, there are several important takeaways:
- Don’t save passwords in your browser - Use an encrypted password manager.
- Use strong passwords and enable MFA - This alone prevents most brute force attacks.
- Audit plugins and themes regularly - Remove unused ones, update outdated ones, and avoid pirated plugins.
- Install a security perimeter - A WAF and server-side antivirus are very worthwhile investments.
- Apply Secure SDLC and secure coding - Security must be built in from the start of development, not added as an afterthought.
- Perform regular maintenance and monitoring - Early detection is far easier to handle than a full-blown incident.
References and Further Reading
- Mengatasi Serangan SEO Judi Online - Surabaya Hacker Link
- Infostealer Spreading Through Fake Google reCAPTCHA - potato.id
- Panduan Penanganan Insiden Web Defacement Judi Online - CSIRT Barito Selatan
- Lesson Learn Penanganan Web Defacement Judi Online - CSIRT Cirebon Kota
This article is adapted from the presentation material “Anti-Gacor dan Malware: Pencegahan dan Perlindungan Injeksi Slot Gacor dan Malware pada Website” by Jonias Fortuna in collaboration with Indocenter & Radnext. The presentation slides can be downloaded here
